Ultimate Switch - Hack Script
Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Integrate into any programming language

A comprehensive suite of integrated tools for authentication, monetization, and user engagement.
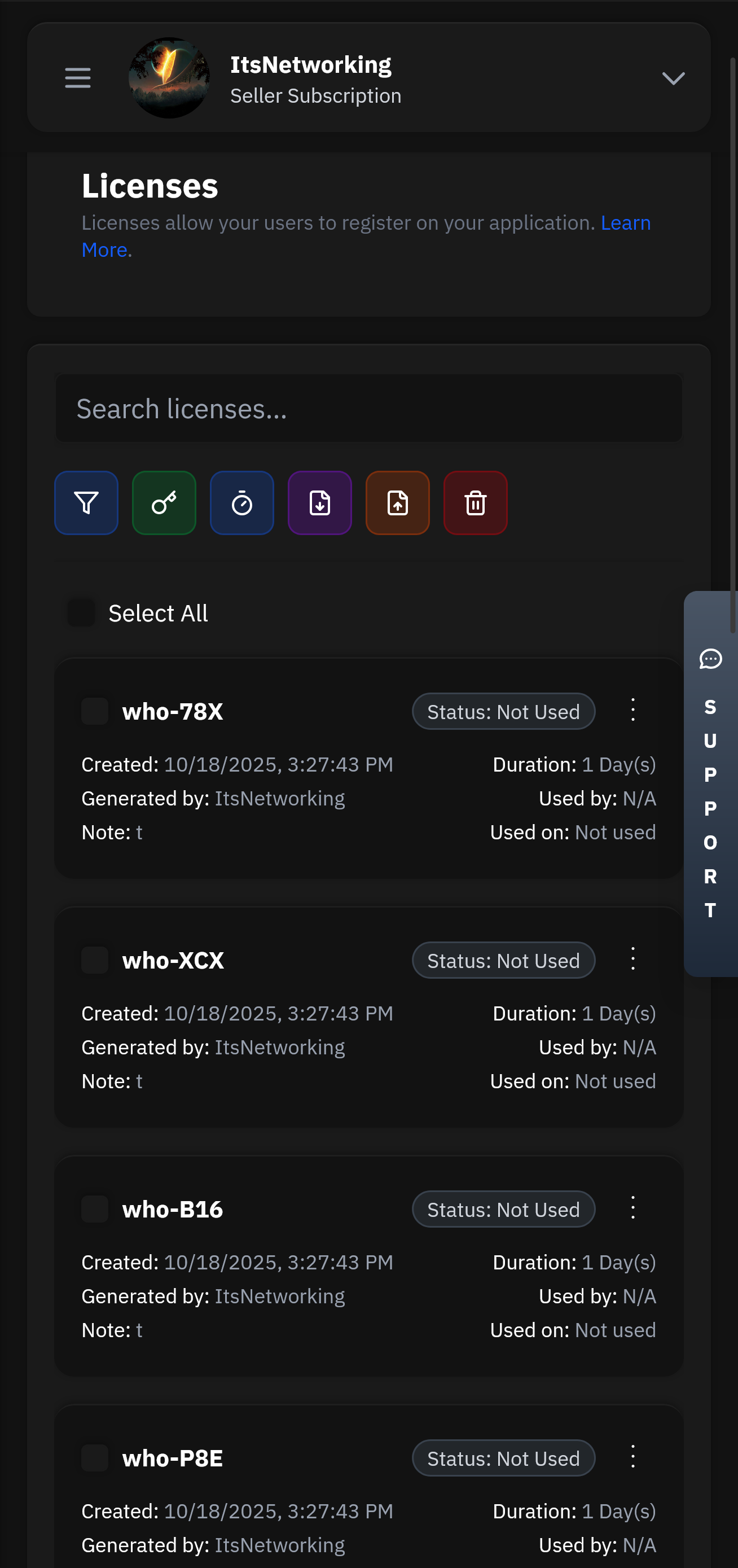
Create and manage user licenses with flexible expiration, trial, and subscription options.
Our lightning-fast infrastructure ensures your authentication requests are processed in under 50ms globally. With 99.99% uptime and redundant systems, your users will never experience delays.
Manage your applications remotely with our powerful Seller API. Update licenses, ban users, modify subscriptions, and monitor usage from anywhere in the world with full administrative control.
Built on a serverless architecture that automatically scales to handle millions of requests. Our global edge network ensures low latency and high availability across 300+ locations worldwide.
There's no question as to why we are the best choice for your business and one of the most used Authentication services.
Head over to our register page to create your account.
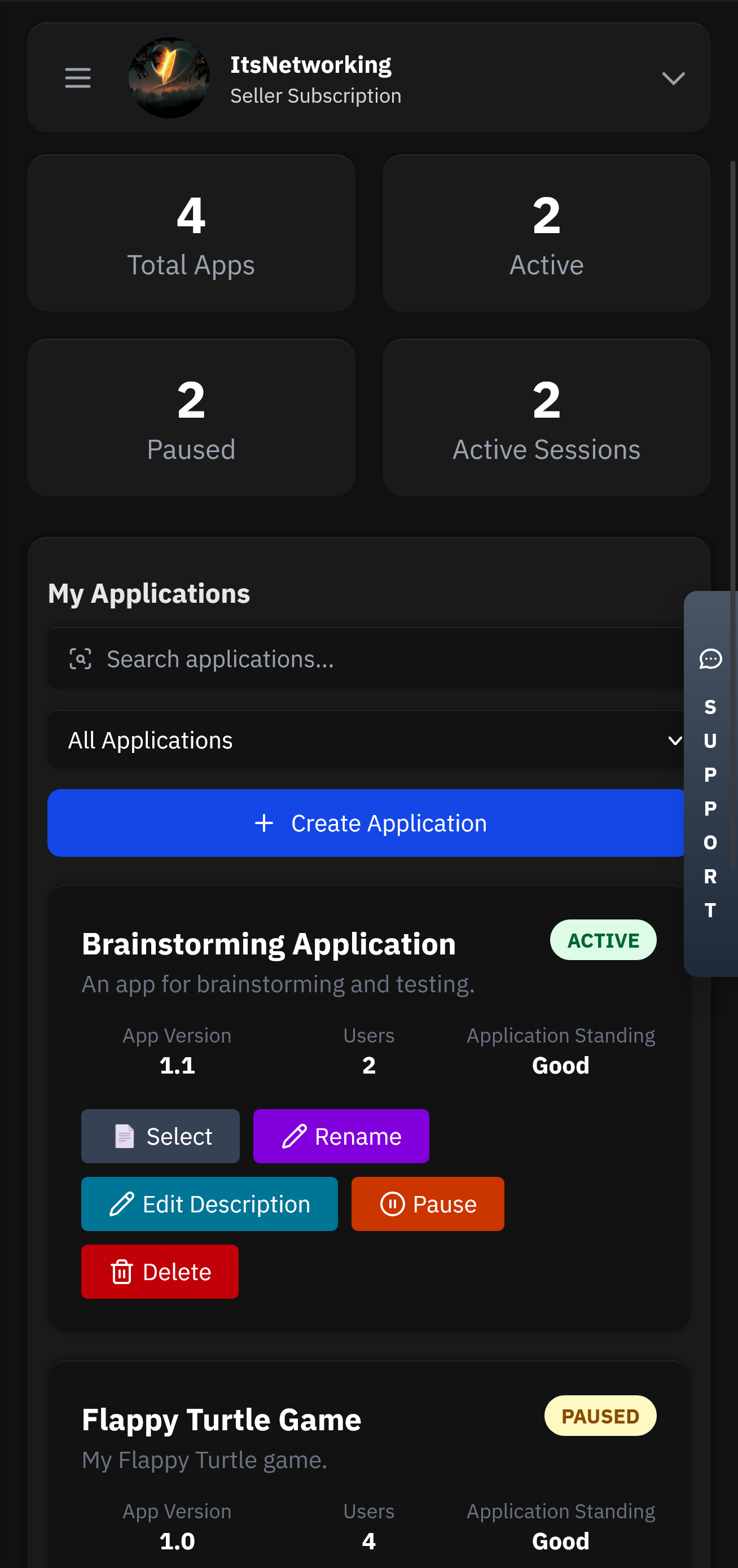
Applications will be the heart of your service. This is where all your users, licenses, chats and more will be stored.
Head over to our GitHub to find our examples and client API files. Simply follow the steps and have authentication up in less than 5 minutes.
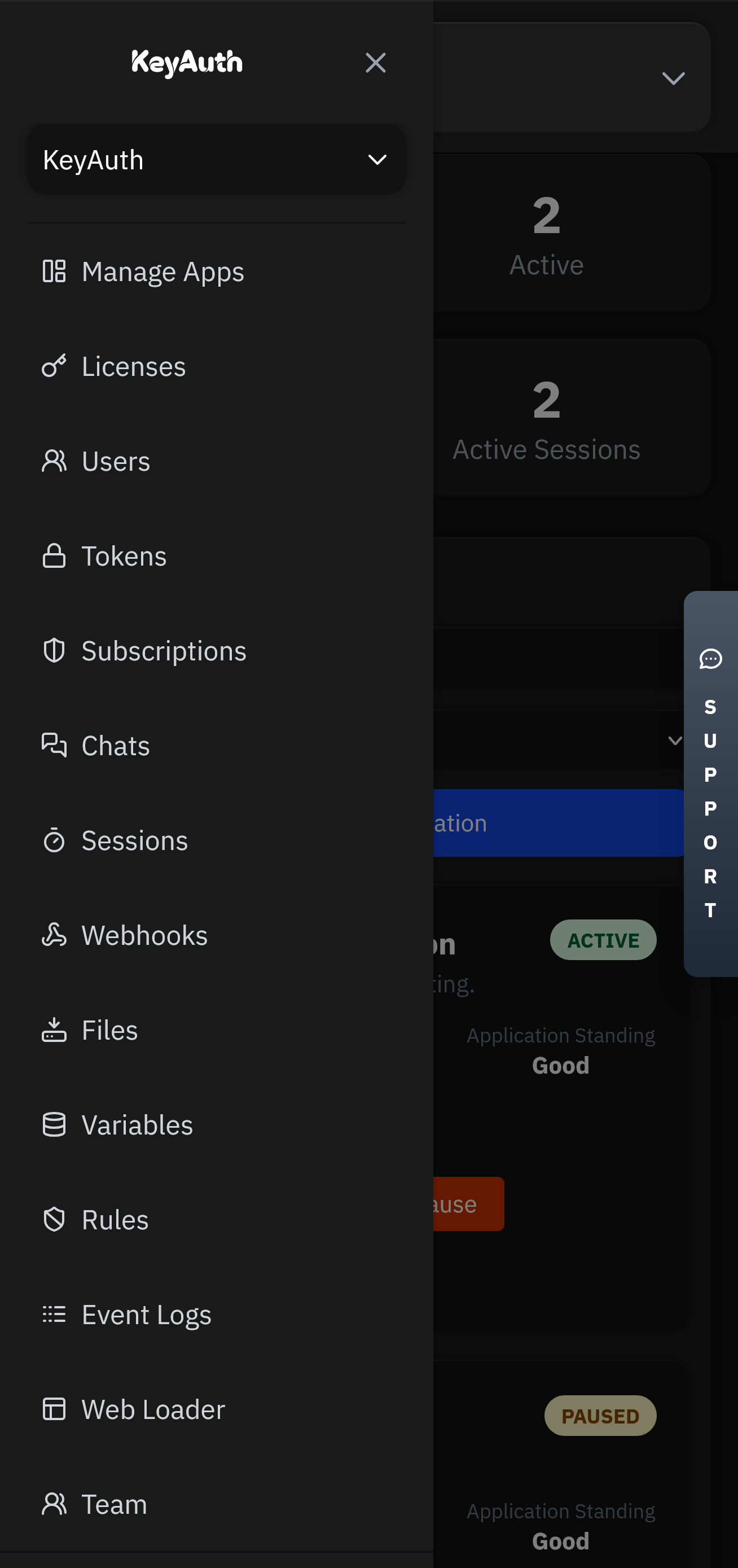
Control your application from anywhere using our mobile app. Manage licenses, chat with users, and view analytics directly from your phone or tablet.
Flexible options for teams of all sizes.
The concept of the "ultimate Switch hack script" represents a significant challenge in the balance between gaming console security and the hacker community's ingenuity. While such scripts can offer users more freedom and flexibility, they also pose substantial risks to intellectual property, security, and the gaming ecosystem as a whole. As technology continues to evolve, both Nintendo and the hacking community are likely to engage in an ongoing battle of wits, with the future of console hacking and security hanging in the balance. Ultimately, understanding the complexities and implications of such hacks is crucial for developing more robust, user-friendly, and secure gaming experiences.
Creating or finding an "ultimate" hack involves deep knowledge of the Switch's hardware and software. The Switch operates on a customized version of the NVIDIA Tegra X1 processor and runs a proprietary operating system. Its security architecture includes several layers of protection, including hardware-based secure boot, a trusted execution environment, and software-based protections.
However, like any complex system, vulnerabilities can and have been discovered. For instance, the Fusée Gelée exploit, discovered shortly after the Switch's release, allowed for the execution of arbitrary code on the console by exploiting a vulnerability in the USB recovery mode. While not an "ultimate hack script" per se, it marked a significant step in Switch hacking.
The Nintendo Switch, a hybrid gaming console released in 2017, has gained immense popularity worldwide. Its unique ability to seamlessly transition between home console and portable handheld modes has made it a favorite among gamers. However, as with any technology, the Switch's popularity has also led to a cat-and-mouse game between gamers seeking to exploit its system and Nintendo's efforts to secure it. This essay explores the concept of the "ultimate Switch hack script," examining the technical aspects, implications, and ethical considerations surrounding console hacking.



Got questions? We've got answers. If you can't find what you're looking for, feel free to reach out to our support team.